Suggested
Reinforcement Learning Optimization in Document AI: How Models Learn From Feedback

SOC 2 (System and Organization Controls 2) is an auditing framework created by the American Institute of Certified Public Accountants (AICPA) that evaluates how service organizations protect customer data. Rather than a certification you earn once and display on a wall, SOC 2 produces a detailed report from an independent CPA firm describing whether your security controls actually work - and for how long they've been working.
The framework centers on five Trust Services Criteria: Security, Availability, Processing Integrity, Confidentiality, and Privacy. Security is always required. The other four are optional, depending on what your customers care about.
For document processing platforms handling sensitive financial or healthcare data, Processing Integrity often matters as much as Security. Processing Integrity is the criterion that proves extracted data is complete, accurate, and authorized - not just protected from hackers.
Enterprise procurement teams treat SOC 2 reports as shorthand for "this vendor takes security seriously enough to prove it." A current Type II report can replace dozens of security questionnaire questions, compressing weeks of back-and-forth into a single document review.
The real value goes deeper than procurement efficiency, though. SOC 2 forces vendors to implement controls they might otherwise skip: formal access reviews, incident response procedures, and change management processes. Think of it like a building inspection - the inspector doesn't make your building safe, but the inspection process ensures you actually installed the fire exits.
For document automation platforms specifically, buyers in lending, healthcare, and financial services often require evidence that extracted data hasn't been tampered with and that extraction logic is version-controlled. That's where Processing Integrity becomes non-negotiable.
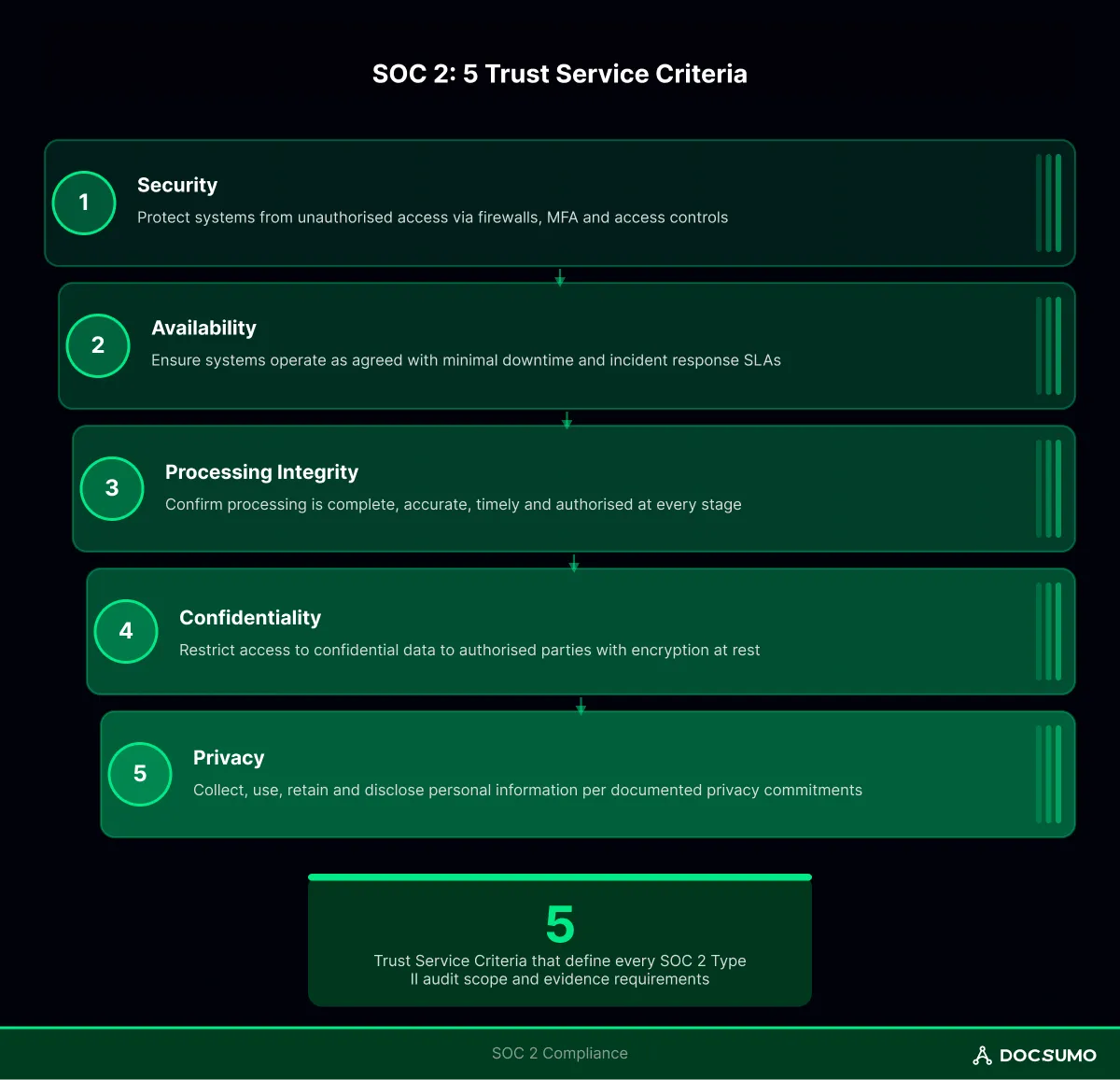
Each Trust Services Criterion addresses a different dimension of how you handle customer data:
SOC 2 Type I evaluates whether controls are properly designed at a specific point in time. It's a snapshot - useful for startups pursuing their first report, but limited in what it proves.
SOC 2 Type II examines whether controls actually operated effectively over a period, typically 6-12 months. A Type I says, "We have a lock on the door." A Type II says "we have a lock, and here's evidence it was locked every night for the past year."
The practical difference matters during procurement. A Type I report might satisfy initial conversations, but security teams reviewing vendors for production deployment almost always ask: "When's your Type II coming?"
The audit unfolds in three phases. Preparation often takes longer than the audit itself.
Before engaging auditors, most organizations run an internal readiness assessment. This involves mapping existing controls to SOC 2 criteria, identifying gaps, and fixing them.
Common gaps include missing access review documentation, informal change management, and incident response procedures that exist only in someone's head.
For example, a document processing platform might have excellent extraction accuracy but no formal process for approving model updates. That's a Processing Integrity gap - changes to extraction logic affect data accuracy, so auditors expect documented approval workflows.
For Type II reports, you'll demonstrate controls operating over your audit window. This means collecting evidence continuously: access review completion records, change tickets with approvals, security training completion logs, and vulnerability scan results.
The evidence collection period is where most first-time audits stumble. Controls that seemed solid turn out to have gaps in documentation. Someone approved a change verbally but never logged it. The quarterly access review happened, but nobody saved the spreadsheet.
The CPA firm samples your evidence, interviews control owners, and tests whether controls work as described. Auditors look for exceptions - instances where a control didn't operate as designed.
Exceptions don't automatically fail your audit. The auditor evaluates whether exceptions are isolated incidents or systemic failures. A single missed access review might warrant a note; discovering that access reviews never actually happened would be a different conversation entirely.
Auditors focus on control design and operating effectiveness. For each control, they ask two questions: Is this control designed to meet the criterion? And did it actually work during the audit period?
Common control areas include:
For document AI platforms, auditors increasingly examine model governance: How are extraction models versioned? Who approves changes? How do you validate that updates don't degrade accuracy?
Tip: Ask vendors for their SOC 2 report before sending a security questionnaire. A well-scoped Type II report often answers 60-70% of standard questionnaire questions.
First-time SOC 2 efforts typically underestimate three things: documentation burden, evidence collection discipline, and the scope of Processing Integrity for data-centric platforms.
This fails when: extraction accuracy is measured only in aggregate (e.g., "95% accuracy") without document-level audit trails showing which fields were extracted, which were corrected, and by whom.
Document AI platforms face unique SOC 2 considerations because they transform unstructured inputs into structured outputs that drive business decisions. The chain of custody matters: from document intake through extraction, validation, human review, and export.
Platforms like Docsumo implement controls architecturally: versioned extraction models, confidence-based routing to human review queues, field-level audit trails, and API-level logging for every data export. This architecture makes Processing Integrity audits straightforward because the evidence collection happens automatically.
Get started with Docsumo's SOC 2 Type II compliant platform →
SOC 2 often coexists with other frameworks, and controls frequently overlap.
The practical takeaway: SOC 2 is often the foundation. Organizations build on it by adding framework-specific controls rather than starting from scratch for each compliance requirement.
SOC 2 isn't a one-time achievement. Type II reports cover specific periods, and enterprise customers expect current reports - typically within the past 12 months.
Continuous compliance requires operational discipline:
Organizations that embed controls into daily operations find subsequent audits straight-forward. Those who treat SOC 2 as an annual scramble spend disproportionate time reconstructing evidence and explaining gaps.
The goal isn't passing audits - it's building the operational maturity that makes passing audits a side-effect of running a well-governed platform.