How To Safeguard Your Business With Security Workflow Automation
Learn about the power of security workflow automation in enhancing your organization's security posture. Explore how automating repetitive security tasks improves efficiency, accuracy, and threat response while reducing costs and scaling operations.

Companies must deal with many issues in the dynamic business landscape, including remote access and compliance. They must also maintain integrity as cyber threats continue to loom, ready to exploit vulnerabilities within organizational systems. They target businesses of all sizes to disrupt operations and cause financial damage. Note that the average cost of a data breach is now at $4.45 million. For a small company, this can mean business closure.
Note that companies increasingly rely on digital solutions to streamline their processes. However, the adoption of such technologies also introduces new security challenges. That’s why secure workflow automation optimizes business processes and fortifies them against potential attacks.
What is Security Workflow Automation?
Security workflow automation refers to implementing automated processes to handle routine security tasks, such as threat detection, incident response, and compliance management. By leveraging tools like Security Orchestration, Automation, and Response (SOAR) platforms, organizations can enhance their security operations, reduce human error, and respond to incidents more swiftly and efficiently.
Key Components of Security Workflow Automation
- Threat Intelligence Integration: Incorporating threat intelligence feeds into automated workflows enables real-time updates on emerging threats, ensuring that the organization’s defenses are always up to date.
- Incident Response Automation: Automated incident response workflows can isolate affected systems, block malicious traffic, and notify relevant personnel, all without manual intervention. This speeds up the containment and resolution of security incidents.
- Compliance Management: Automation helps maintain compliance with industry regulations by continuously monitoring and enforcing security policies. Automated reporting and audit trails simplify compliance management and reduce the risk of non-compliance penalties.
- User and Entity Behavior Analytics (UEBA): Integrating UEBA into security workflows allows for the detection of abnormal behavior patterns, providing early warning signs of potential security breaches.
Benefits of Security Workflow Automation
Implementing secure workflow automation can offer numerous benefits for your business. It can enhance various aspects of operations and ensure robust protection against cyber threats.
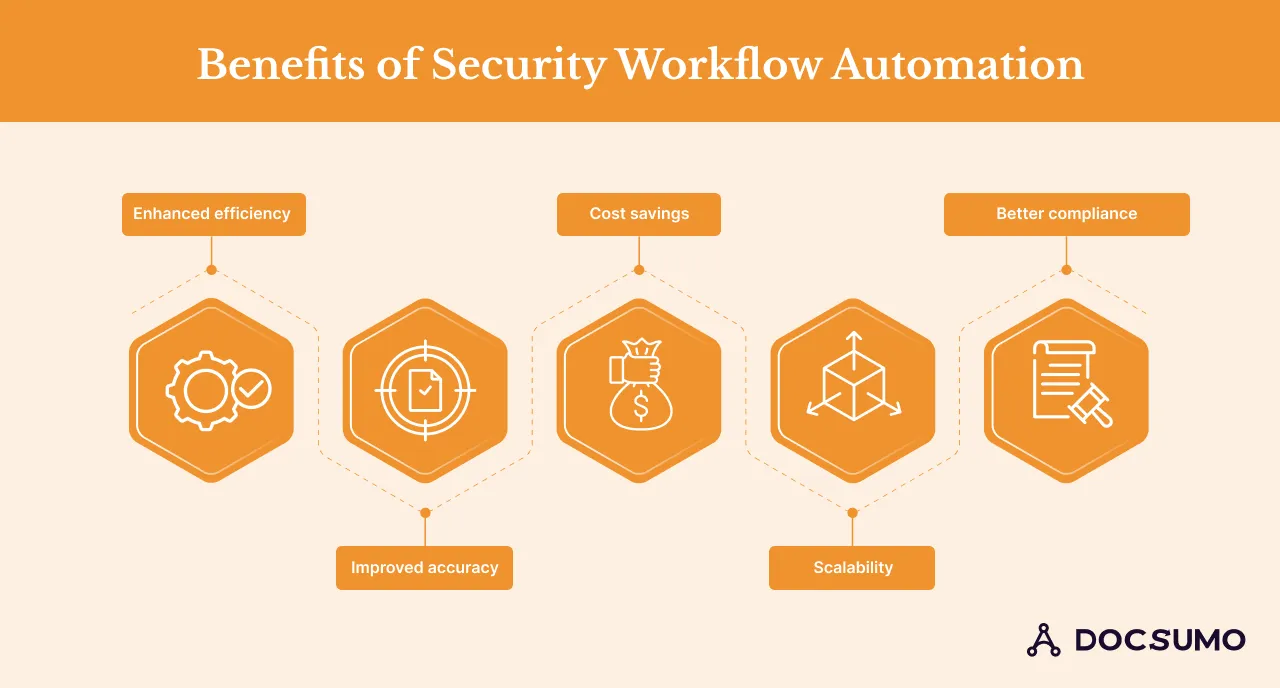
1. Enhanced efficiency
Automating mundane tasks reprieves employees to focus on activities that bring greater value to the company. For example, employees can focus on strategic initiatives that drive growth and innovation. Such activities will allow businesses to boost their productivity and further improve processes.
Consider communication tools that integrate seamlessly with your existing security infrastructure. Some providers have mobile devices that support secure and automated business processes.
2. Improved accuracy
Business mistakes can be costly. Automation eliminates the possibility or risk of human error. Manual processes are prone to mistakes. Secure workflow automation ensures that tasks are performed correctly and uniformly every time.
3. Cost savings
For-profit businesses always seek ways to cut costs to boost their bottom line. Most companies spend a huge chunk of their resources on labor costs. With automated workflows in place, there’s no need for manual labor for repetitive tasks. It also reduces the time to complete tasks and the likelihood of errors necessitating corrective actions. These efficiencies translate into good profit margins and better resource allocation.
4. Scalability
Running a sustainable business means the ability to scale operations without additional investments. It’s important to know that growth means the volume and complexity of tasks will also change. Automation workflows allow your business to accommodate these changes with minimal changes in staffing or resources.
5. Better compliance
Secure automation helps ensure compliance with industry regulations and standards. A compliance officer can program automated systems to adhere to regulatory requirements, providing an audit trail and proper process application.
Best Practices for Secure Workflow Automation
Here’s how to ensure secure workflow automation to protect your business and enhance efficiency:
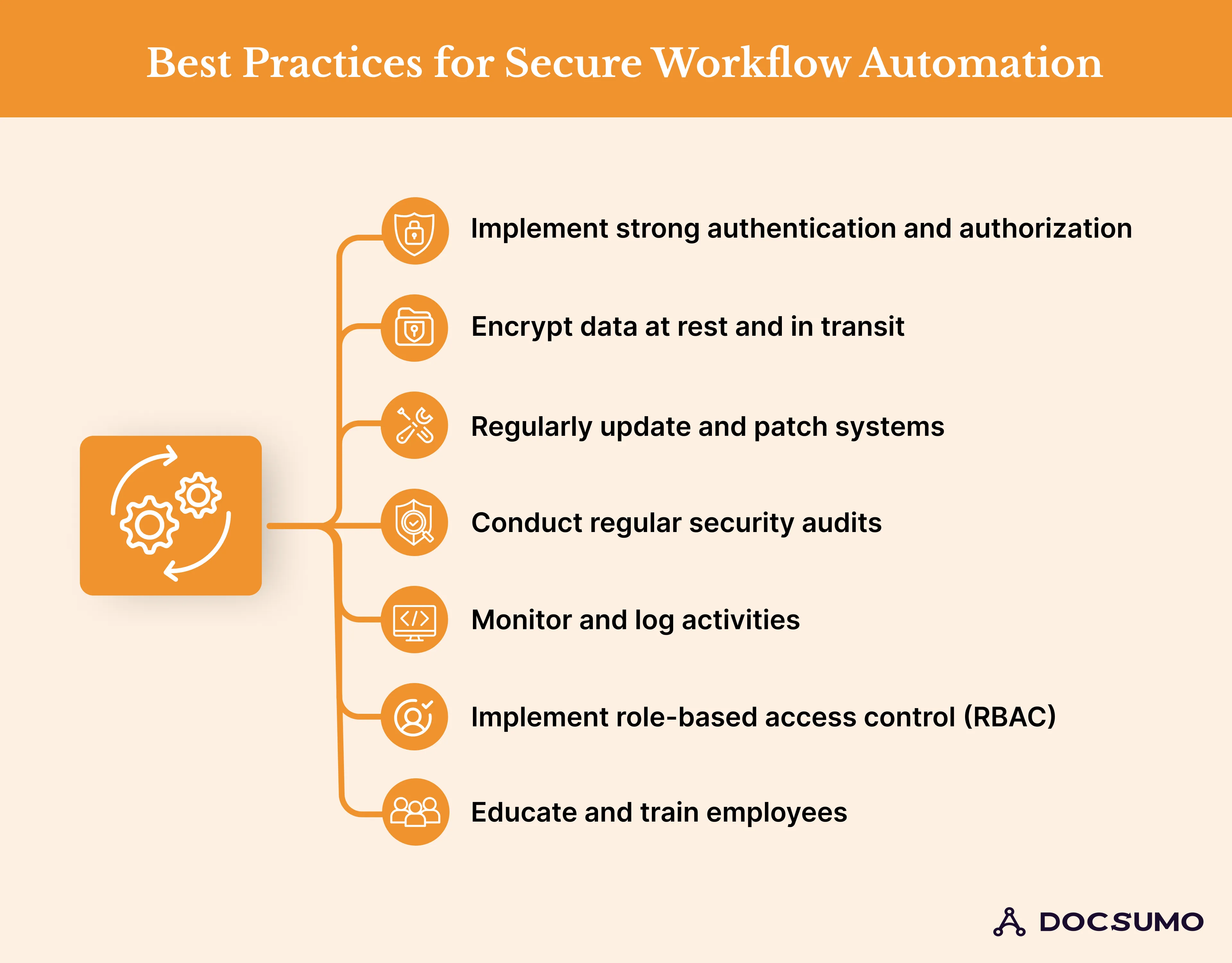
1. Implement strong authentication and authorization
Implementing a secure workflow means setting up stringent authentication mechanisms to prevent unauthorized access. One way is to implement multi-factor authentication (MFA). Equally important is defining access protocols to ensure that only authorized staff can work on specific workflows.
2. Encrypt data at rest and in transit
Encryption plays a pivotal role in fortifying automated workflows. Ensure that all data, both at rest and in transit, is fortified with robust encryption standards. This is a key measure to prevent interception of sensitive information.
3. Regularly update and patch systems
Using outdated software creates vulnerabilities that cyberattacks can exploit. To close any security vulnerabilities, update and patch all systems involved in your automated workflows. Establish a routine schedule for updates and ensure that patches are applied promptly.
4. Conduct regular security audits
Workflow automation should undergo regular security audits to identify and address potential weaknesses. Conduct internal and external audits to evaluate your security posture. Use the data to improve your security measures.
5. Monitor and log activities
Use advanced monitoring tools to analyze logs and identify potential threats in real time. This helps you detect and respond to suspicious activities promptly.
6. Implement role-based access control (RBAC)
This control is an efficient security strategy that limits system access based on organizational roles. By assigning permissions based on roles, you can minimize unauthorized access. Employees have access only to the information necessary for their job functions.
7. Educate and train employees
Human error is often a significant security risk. A report found that 74 percent of all breaches involved the human element. This highlights the imperative for comprehensive employee education and training on security best practices.
Train and educate your employees on the role of security in workflow automation. Provide regular training sessions on best practices and how to respond to security incidents. Employees can be the first defense against security attacks and reduce the risk of breaches.
Leverage Secure Workflow Automation Tools
Investing in reliable and secure workflow automation tools is crucial for safeguarding your business. Look for automation tools that offer security features, such as advanced access controls.
Take action today to secure your workflow automation and fortify your business against potential risks. Embrace secure automation tools and propel your business toward a more secure and efficient future.